发现两个文件头HEX为c8 04 76 63 的文件应该是资产清单
https://ntmj-patch.uj.com.tw/Android_AssetBundles/251001_ntmj/Android
https://ntmj-patch.uj.com.tw/Android_AssetBundles/251001_ntmj/Raw/Raw
没见过文件头也不是可读ASCII没搜到啥资料望大佬指点
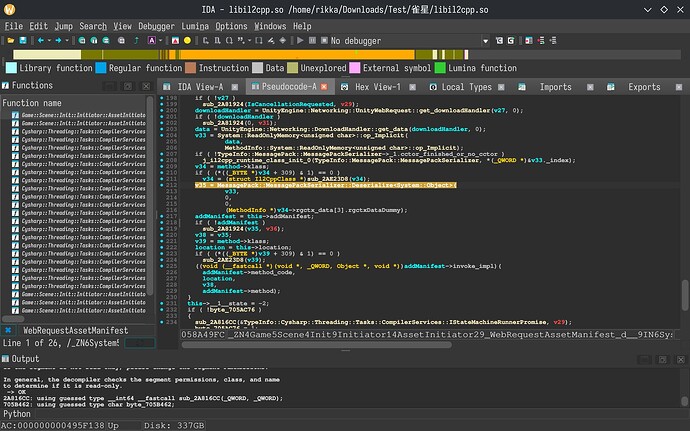
感觉就是序列化了下,看下il2cpp里面的伪代码就知道了吧 ![]()
尝试解析了一下参考了一些资料似乎是MessagePack ExtType?自定义结构
struct MessagePack_ExtensionResult_o {
struct MessagePack_ExtensionResult_Fields fields;
};
struct MessagePack_ExtensionResult_Fields {
int8_t _TypeCode_k__BackingField; // 0x00
uint8_t _padding[7]; //
struct System_Buffers_ReadOnlySequence_byte__Fields _Data_k__BackingField; // 0x08
};
struct System_Buffers_ReadOnlySequence_byte__Fields {
Il2CppObject* _startObject; // 0x00
Il2CppObject* _endObject; // 0x08
int32_t _startInteger; // 0x10
int32_t _endInteger; // 0x14
};
找出的一些屎不知道有没有用
99吧,再lz4解压就行了
原始数据.zip (387.9 KB)
单独dump出data数据到一个文件尝试lz4解压好像也不行
import msgpack
import lz4.block
import json
import struct
import sys
def decode_lz4(data):
s = 0
o = 0
m = data[0]
if m == 0xD2:
s = struct.unpack(">I", data[1:5])[0]
o = 5
elif m == 0xD1:
s = struct.unpack(">H", data[1:3])[0]
o = 3
elif m == 0xD0:
s = data[1]
o = 2
else:
o = 0
return msgpack.unpackb(
lz4.block.decompress(data[o:], uncompressed_size=s),
strict_map_key=False,
ext_hook=ext_hook,
)
def ext_hook(code, data):
if code == 99:
return decode_lz4(data)
return msgpack.ExtType(code, data)
def bytes_to_hex(obj):
if isinstance(obj, bytes):
try:
return obj.decode("utf-8")
except:
return f"<HEX>{obj.hex()}"
if isinstance(obj, dict):
return {str(k): bytes_to_hex(v) for k, v in obj.items()}
if isinstance(obj, list):
return [bytes_to_hex(i) for i in obj]
if isinstance(obj, msgpack.ExtType):
return f"<ExtType code={obj.code}>"
return obj
def process(p):
with open(p, "rb") as f:
b = f.read()
with open(p + ".json", "w", encoding="utf-8") as f:
json.dump(
bytes_to_hex(msgpack.unpackb(b, strict_map_key=False, ext_hook=ext_hook)),
f,
ensure_ascii=False,
indent=4,
)
if __name__ == "__main__":
process(sys.argv[1])
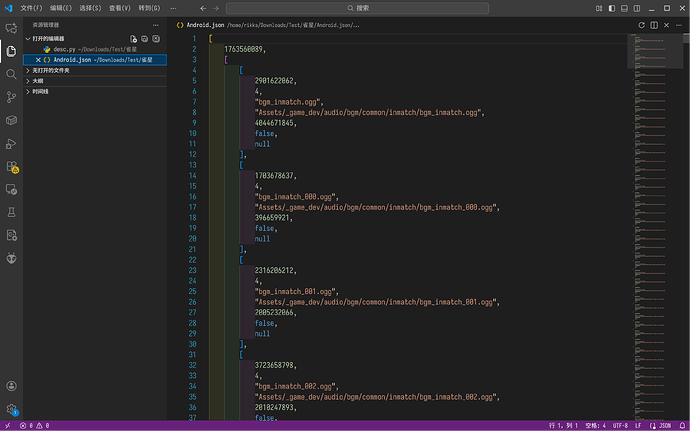
不过解析出来没有字段,你可以看着加上
多谢指点 ![]()
还有ext_hook我也是没想到